Empowering business without compromising security and compliance

Collaborative governance brings in new capabilities to enable business teams and IT to work together while ensuring security, transparency and governance around integrations. Collaborative governance combined with Transparent UX and Zero DevOps defines Workato’s Digital Native Architecture (DNA).
Teams and Roles
Workato Teams allows account owners or admins to invite and add other members from inside the company (e.g. employees, contractors) or outside the company (e.g. consultants, partners) to work together and collaborate.
Team members are added as collaborators. One Workato account may also be a collaborator in multiple teams. As a collaborator in a team, you share a private workspace with other team collaborators, enabling multiple users to work together to create recipes and share the same resources.
All recipes and resources linked to those recipes e.g. lookup tables, connections persist with the Workato account that owns the team. This makes it easy for collaborators to join, contribute and leave without disrupting the work of other collaborators in the team, or the functionality of the recipes.
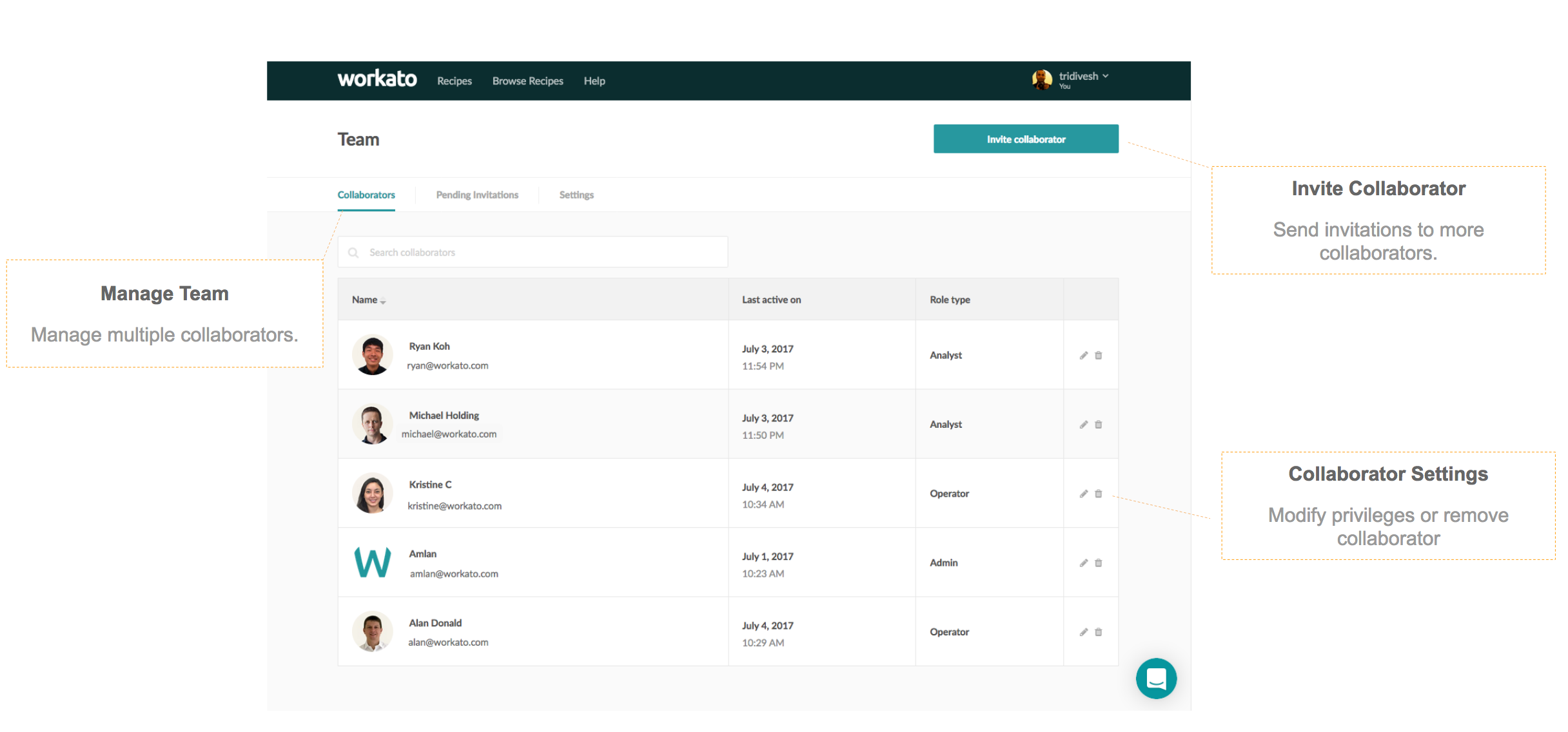
Manage Multiple Collaborators for a Team
- Account owners and admins can easily onboard or offboard collaborators from a team. For example, a new employee can be added as a collaborator to the marketing team, while an outgoing contractor can be removed from the team.
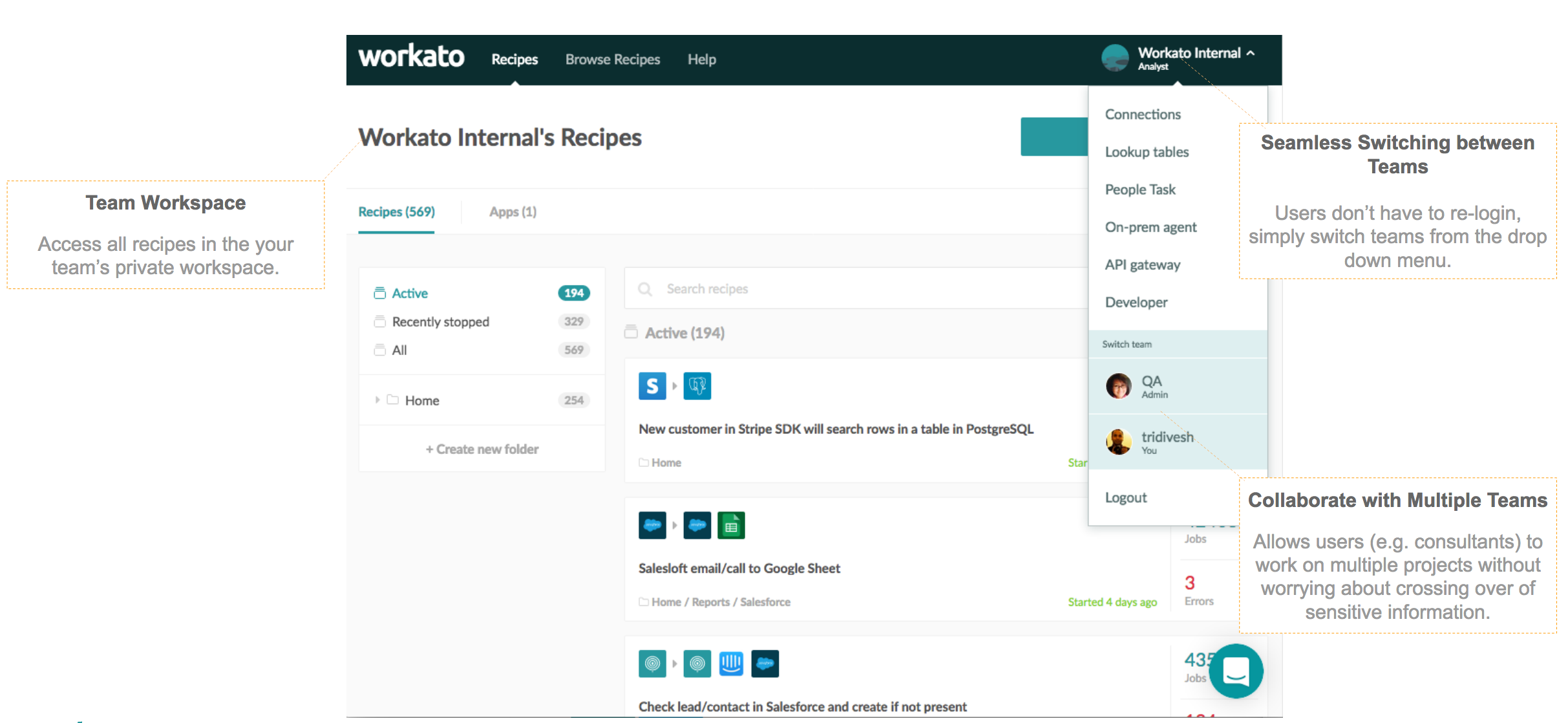
Easily Collaborate with Multiple Teams
- Employees within a company or consultants working with multiple customers can collaborate with multiple teams.
- Since the workspace for each team is private and not shared with other teams, collaborators are not burdened with managing the explicit separation of their recipes across multiple teams.
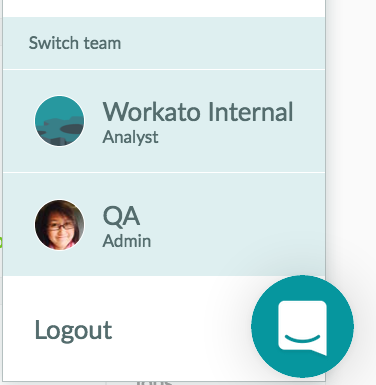
Effortless switching between teams
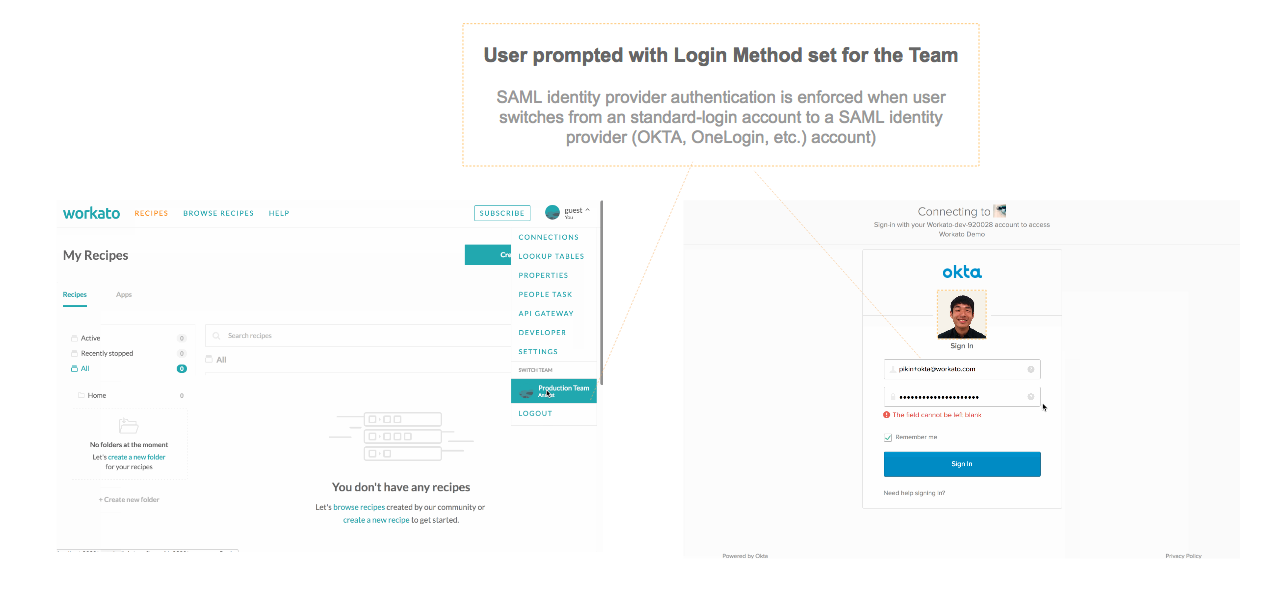
- As a collaborator working with multiple teams, it is essential that you are able to switch from one team to another effortlessly.
- The experience of switching between teams is very similar to the switching between accounts in Gmail.
- In most cases, the user is not required to re-authenticate their account unless the team they are switching to is SSO enabled. In that case, the user will be prompted to login with their OKTA, OneLogin or other SAML identity provider credentials.
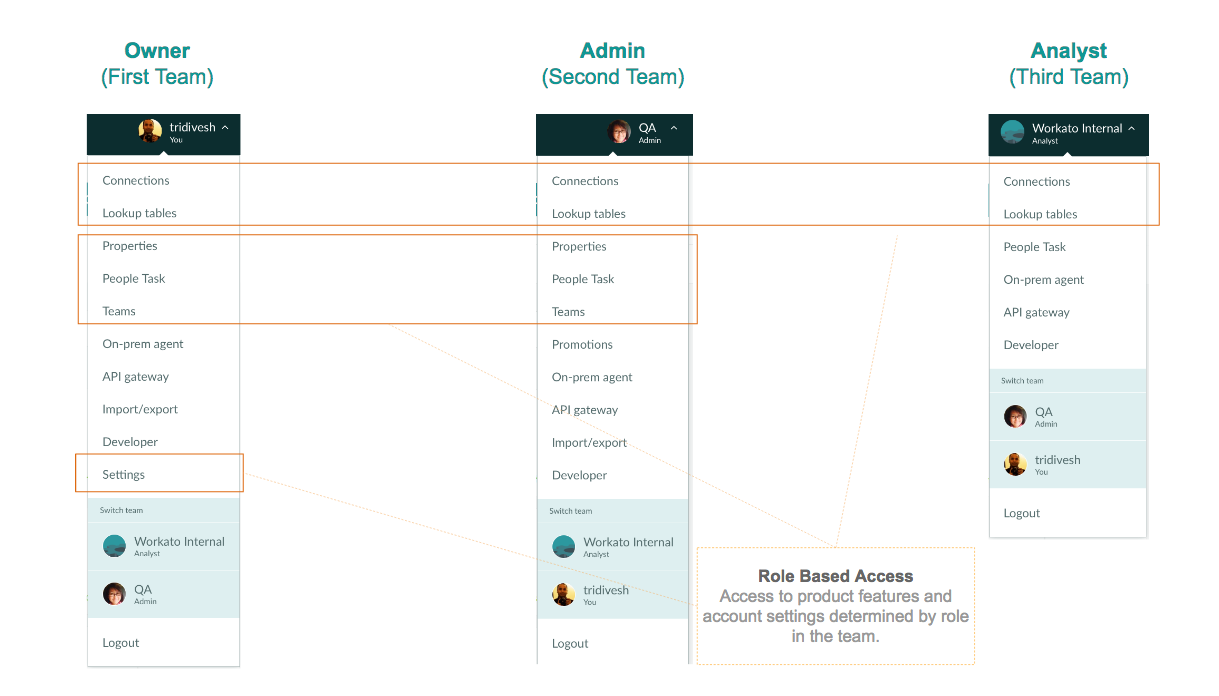
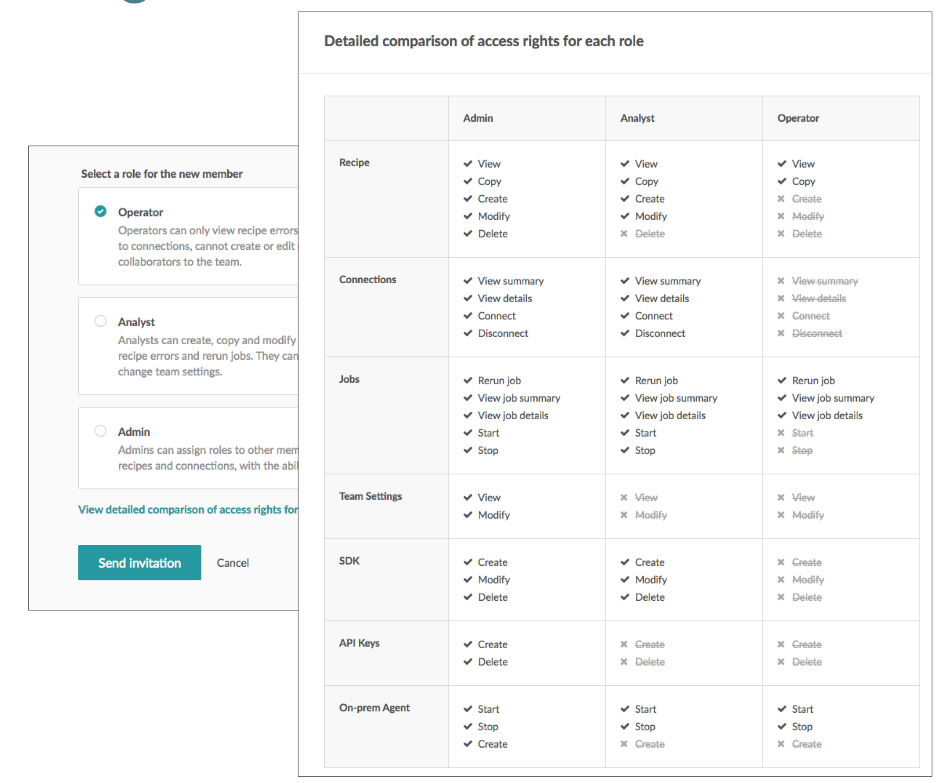
Better Governance with Role Based Access
Role based access control enables Workato admins to limit users to only the set of features and privileges they need for their work.
Admins can assign operator roles to members responsible for runtime operations only i.e. start, stop and resume paused jobs, but not create or modify recipes. For members of the team that will collaborate by creating, updating and testing recipes, the Analyst role encompasses the required privileges. Admins can also delegate the admin responsibilities to other users using the more powerful Admin role.
This role based framework allows admins to choose from a set of predefined roles that can be customized across 7 different contexts (recipe, connections, jobs, on-prem agent, SDK, team settings and API keys) and 24 different actions (create, modify, delete, copy etc.). For more advanced requirements, custom roles (other than the preset roles of Operator, Analyst, and Admin) can be defined using a combination of context and actions.
Enforcing security and compliance with SSO
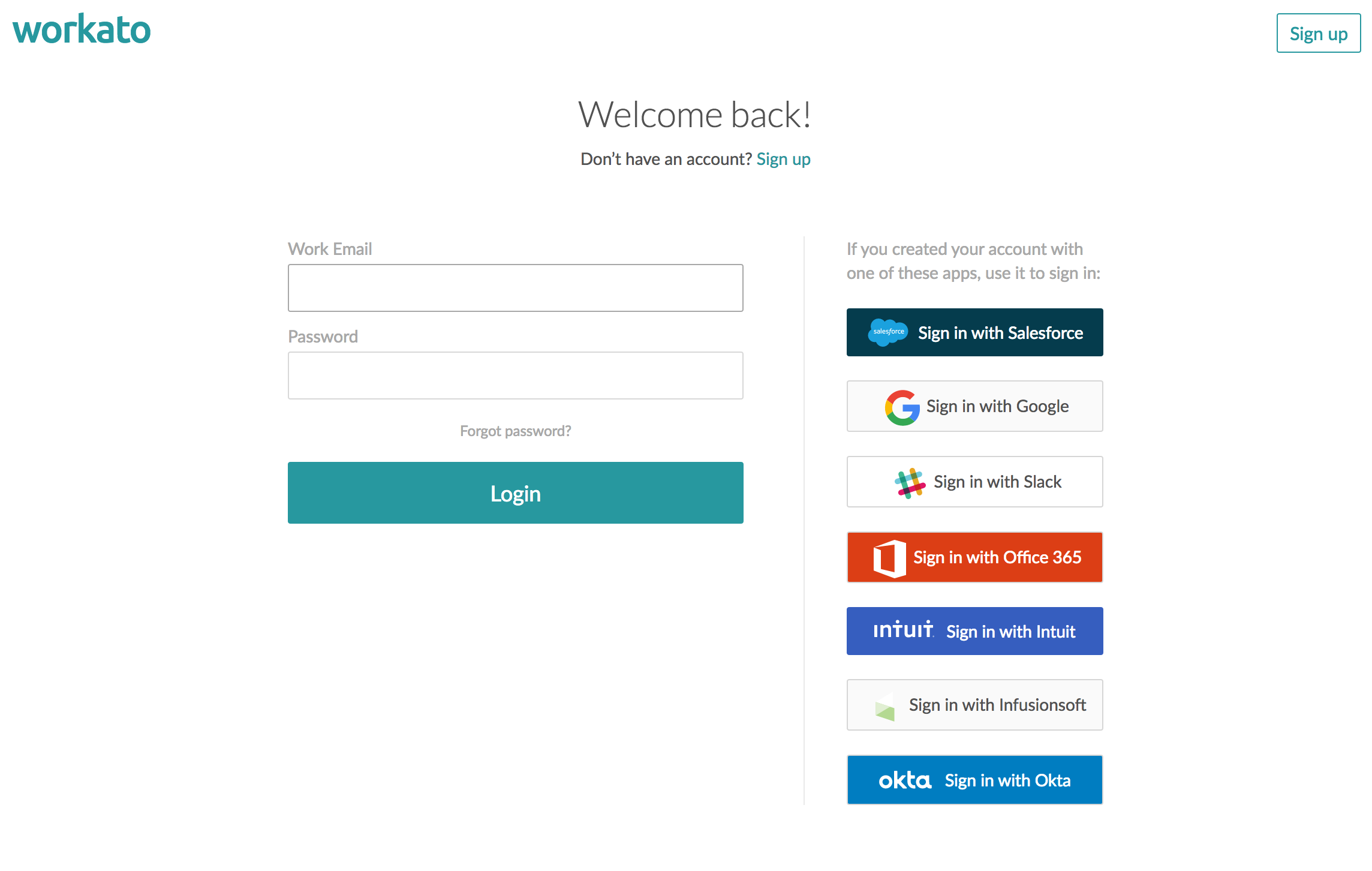
Single Sign On (SSO) platforms e.g. OKTA, OneLogin provide solutions that are efficient and secure for both users and IT. SSO eliminates the need to set, remember and manage username and passwords for multiple applications thereby improving user productivity and, most importantly, helping IT enforce security and compliance requirements.
With the launch of SSO support for OKTA, OneLogin and other SAML identity providers, Workato users can now sign up/login using a single digital identity such as their OKTA credentials.IT admins can also manage provisioning, de-provisioning, and permissions of accounts for Workato. In addition to OKTA, Workato supports multiple other SSO platform identities e.g. Salesforce, OneLogin, Google, Slack, Office 364 and any SAML provider.
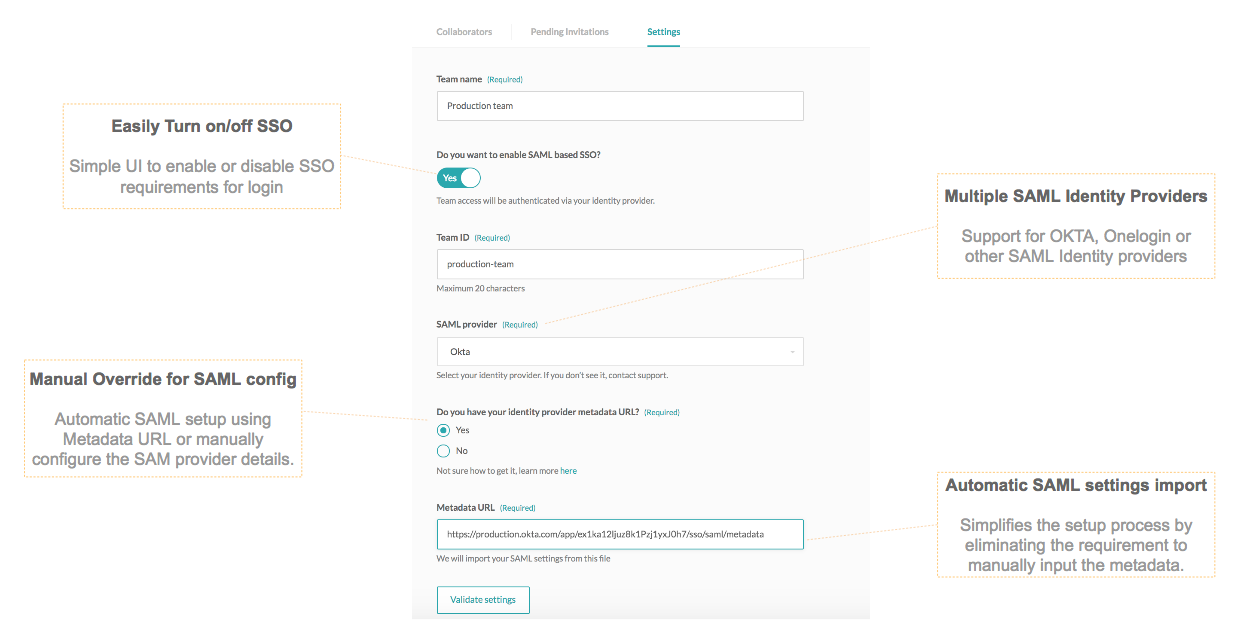
On the administration page of a Workato Team, an option to choose a SAML identity provider is available. Workato account administrators can configure the SAML identity provider details on this page. It also provides Just-in-Time (JIT) provisioning, eliminating the need for team admins to create Workato user accounts on behalf of team members.
- Users signing up for a Workato account via SAML SSO are automatically added to the organization’s team.
- Default Workato profile and role (operator) is automatically set using SAML attributes.
Seamless switching between login methods
SAML is usually expected to be enabled when multiple users are already using Workato and created content (recipes, lookup tables, account properties, settings etc.).
Workato allows users to transfer their history from a standard login (username/password) to the new login credentials using SSO.This powerful feature allows seamless migration of users from one login method to another. It also eliminates the challenge of onboarding users again and migrating history from one account to another. As long as the Workato account uses the same binding email, switching from one login method to another is effortless.
Turning on and Turning off SSO
Workato provides the flexibility of converting accounts from SSO based authentication to standard (username/password) authentication.
Turning on SSO: When SAML based SSO is enabled, all collaborators (Workato accounts) in a team will be required to authenticate using their SAML identity provider credentials e.g. OKTA.
Turning off SSO: When SAML based SSO is disabled, all collaborators (Workato accounts) in a team will be required to authenticate using standard login credentials (username/password).
Powering Agile Iterative Development
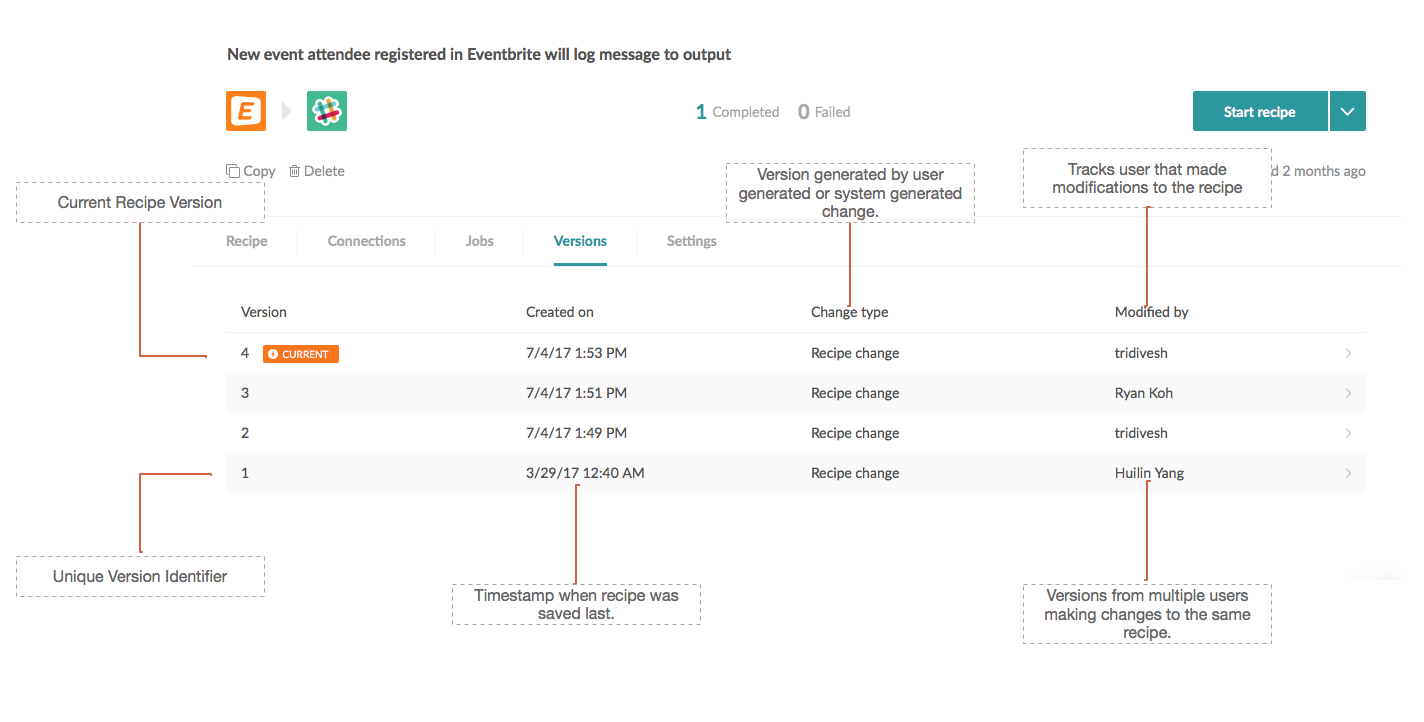
Google office and Atlassian products (Confluence, JIRA) have pioneered the collaboration models to power agile iterative development. Workato’s recipe building process powers collaboration in a similar way by auto-versioning and auto-logging all changes made to a recipe. With the latest release, the same auto-versioning and auto-logging capabilities are available in a multi-user team environment.
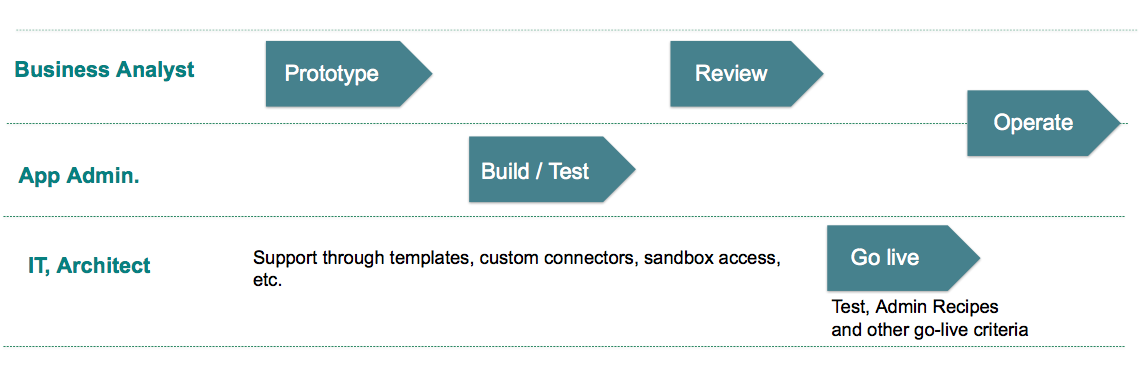
For example, a business analyst (subject matter expert for Sales) can build the prototype for the recipe with a linear process flow. The App Admin can then add standard business rules, data validation checks (e.g. referential integrity), and other modules. Moving forward, the business analyst can then test the fully built recipe and send it to the IT admin to release it to production. In this process, 3 different users would have made some changes to the same recipe.
The auto-tracking and auditing of changes provide complete transparency on the latest changes and versions of the recipe from each iteration. It also gives you the ability to track issues, retrace your steps to resolve unwanted changes and be able to restore a healthy & functional version of your work.
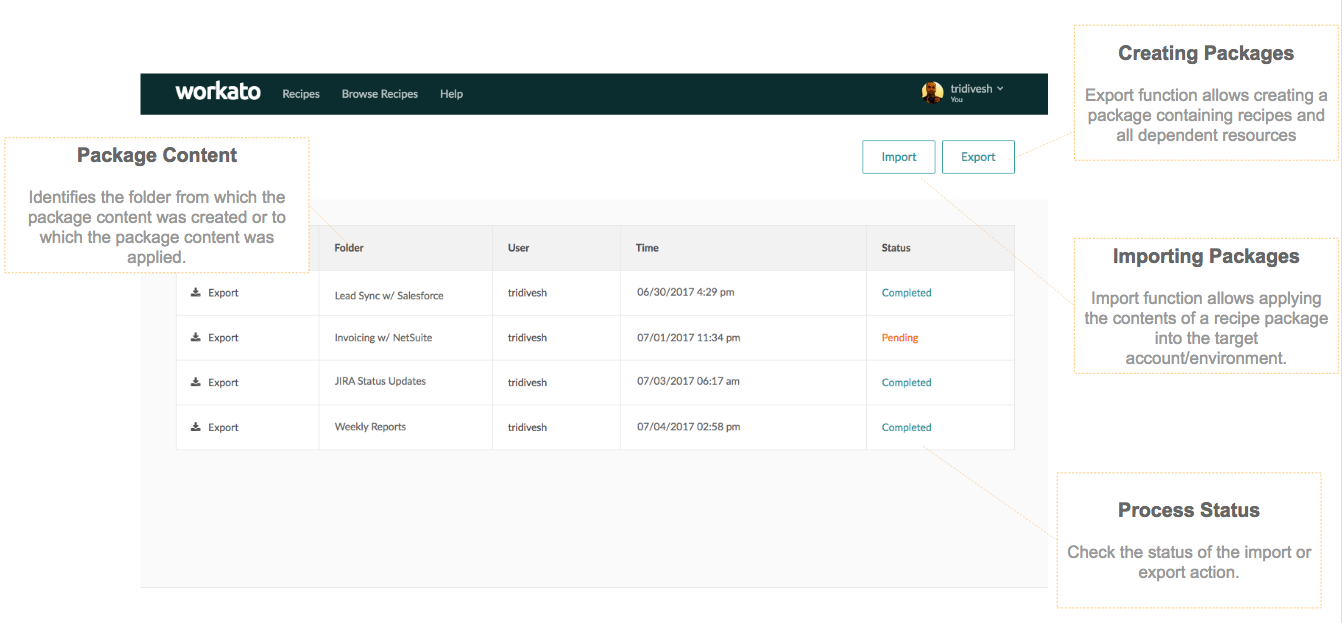
In addition to preserving one’s work, users may be required to move recipes from one account to another or, as a part of the release process, promote recipes from development to testing, and testing to production environments. Recipe Packages are an extremely powerful and useful tool for moving recipes in bulk.
They are used to seamlessly move recipes and all dependent resources (e.g. connections, lookup tables, account properties etc.) across dev, testing and production environments.
Recipe Packages
- Can be easily moved between environments/accounts saving time and eliminating errors.
- Can be checked into any version control system e.g. Git, thus enabling integration with existing release management processes in an organization.
Admin Super Powers
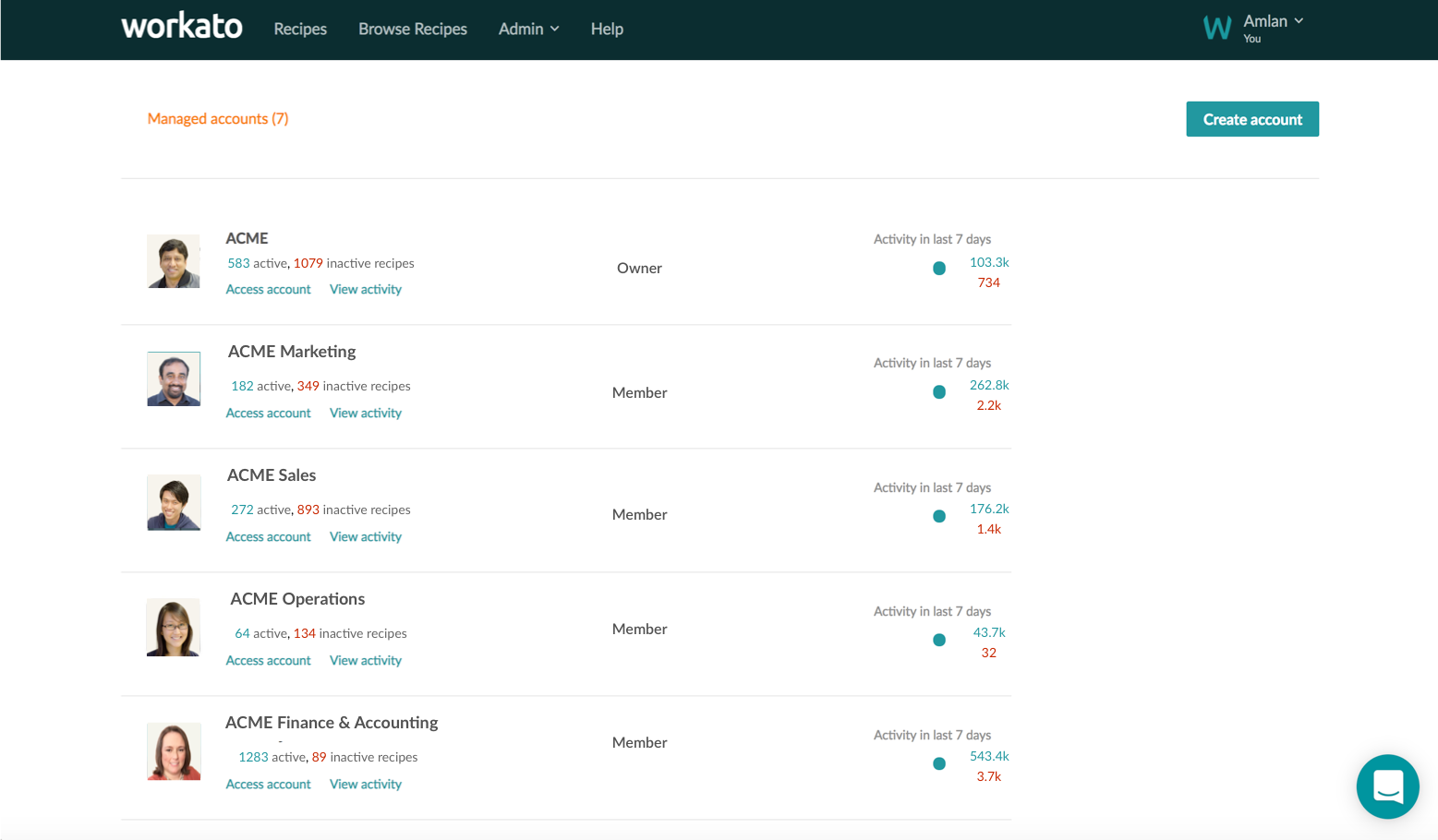
Workato supports additional admin roles that can monitor usage and activity of multiple users and multiple teams in an organization.
For example, in the ACME company, the super admin can create multiple teams (marketing, sales, operations, finance, and accounting) and monitor the usage of each team. The Admin console provides the ability for Super Admins to view usage stats vis-a-vis job history, transactions, recipes, successful and failed recipes, active and inactive recipes. Furthermore, users can assume admin privileges for accounts or delegate admin privileges to other members to control and scale operations.
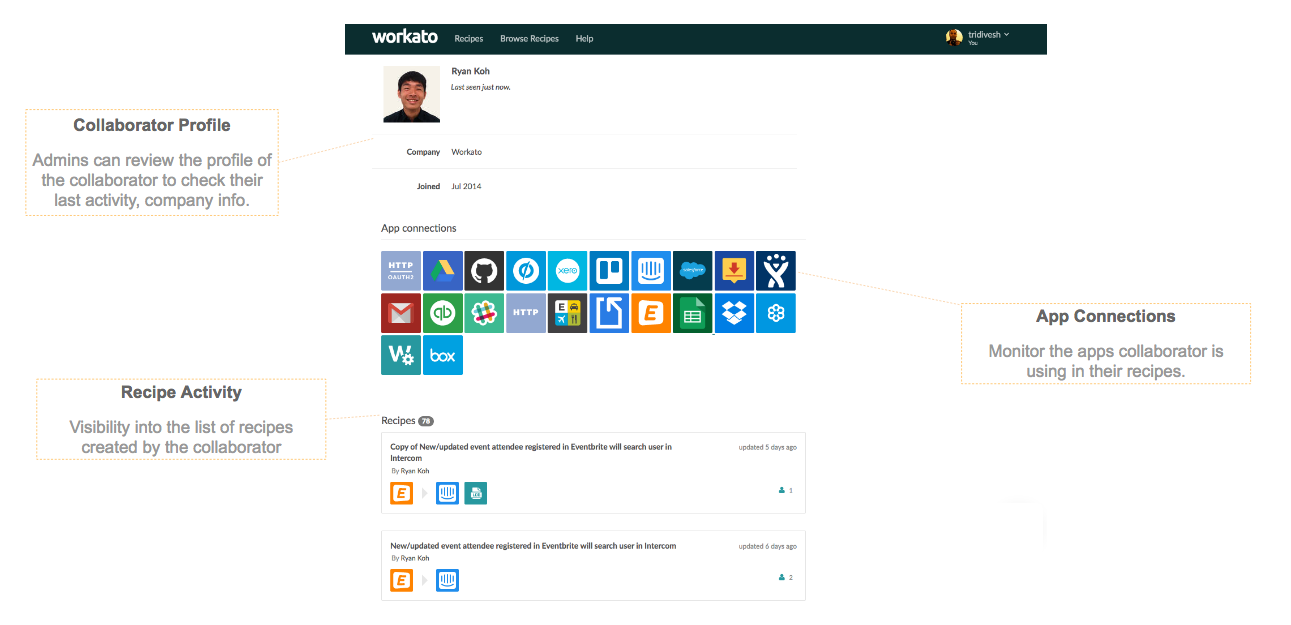
Admins also have access to monitor and review the profile of each collaborator including app connections, recipes created, jobs, transactions.
Data Protection
Workato provides end-to-end encryption where all the data is transmitted securely over SSL and all customer data is stored encrypted. It also provides data masking capabilities to mask any sensitive information, like PII information.
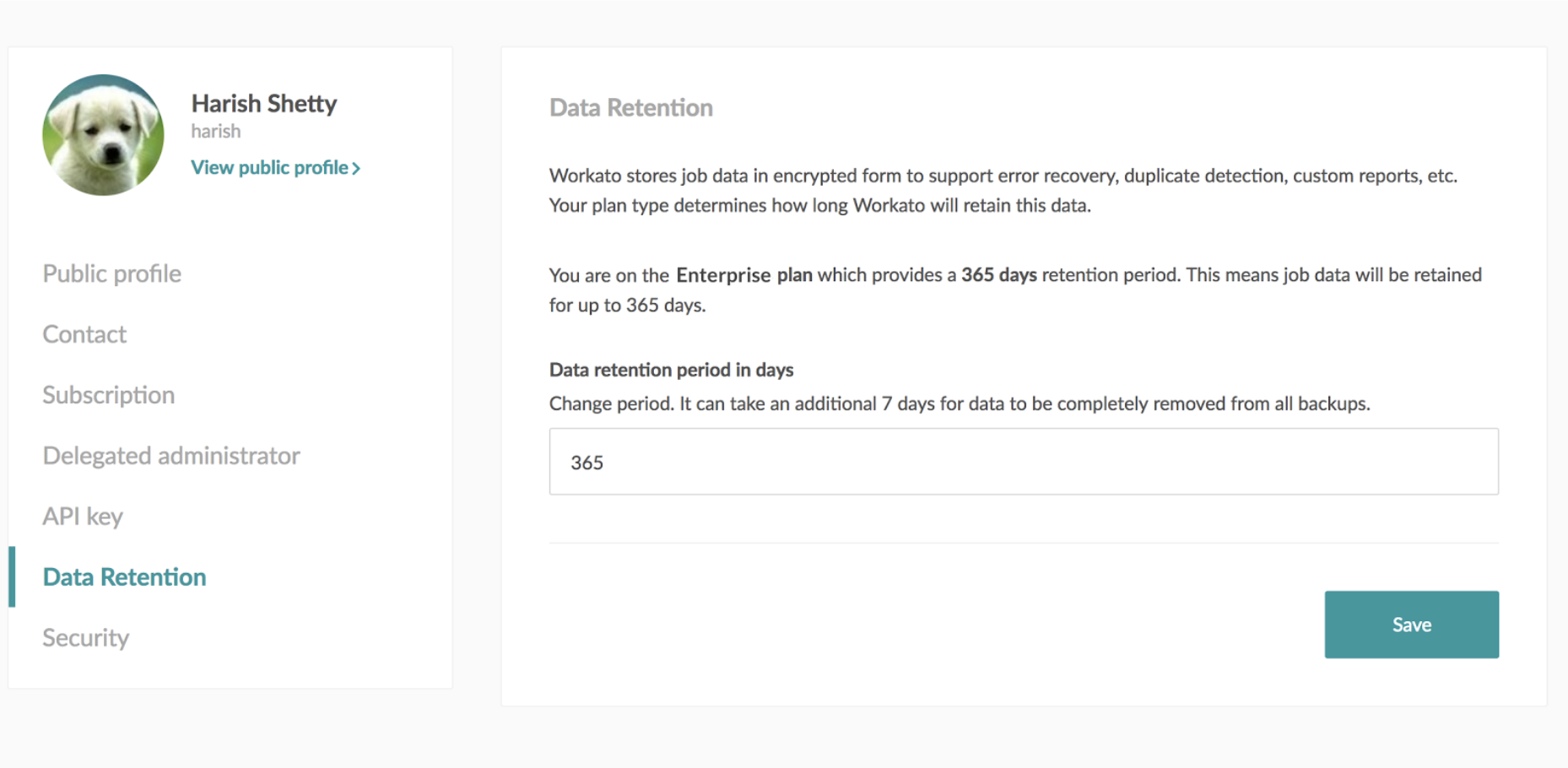
This update provides the ability to configure a data retention period as well for the data that is stored on Workato servers. Shortening the retention period is typically done for sensitive data while having a longer retention period helps troubleshoot errors.
Interested in seeing the Turing Release in action? Setup a time with our friendly Integration Advisors.