Take control of your data with Workato’s new Australia data center
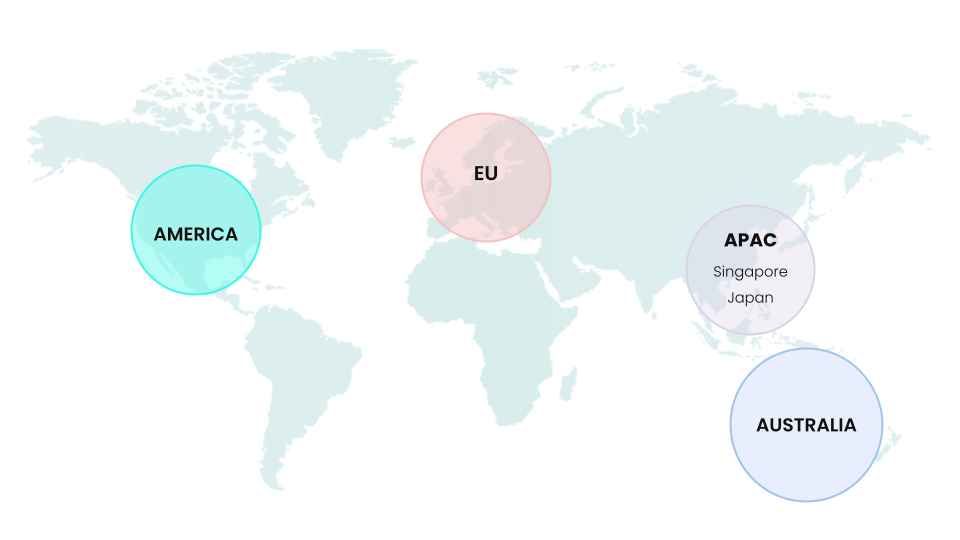
We are very excited to announce the availability of our new Australia data center, in addition to our existing data centers in the US, Europe, Singapore and Japan. Our growing customer base in Australia and New Zealand regions can now choose where their Workato account is hosted.
The new Australia data center allows organizations in the region to better utilize the benefits of the Workato platform by offering closer geographic proximity to their data.
Key components of the Australia Data Center include:
- Location in Australia, leveraging multiple data centers and cloud infrastructure provided by Amazon Web Services, built with the same high-availability architecture design as Workato’s US infrastructure;
- The option for customers to keep all of their data in the Australia data center facilities located within the region;
- 100% in-region data locality, with no replication or backup to US data centers;
- Infrastructure and code base updated on the same schedule as the US;
- A facility that is operational and available to Australian customers with immediate effect.
Data storage
The new data center makes it easy for you to meet your internal policies on data storage location and regulatory requirements mandated by the government.
You determine the data storage location by signing up for an account in the data center region of your choice. If you have signed up in the Australia data center, then all your data is processed and stored in the Australia data center. Examples of data and metadata include recipes, connections, shared assets like lookup tables, and job logs.
No data transfer between data centers
Our data centers do not transfer customer data to a data center in another region. Workato regional data centers are standalone infrastructure to serve customers and users in that region. This provides data storage and processing isolation in each region to meet the data protection requirements of the customers.
Instant platform updates
Workato’s innovation in supporting multiple data centers includes the capability to deploy all platform updates at the same time in all regions, including the US, Singapore, Japan, the European Union and Australia.
Typically SaaS providers roll out region by region to mitigate risks in case a software update accidentally disrupts the service. But Workato’s robust software development practices and advanced infrastructure management let us deploy Workato platform updates simultaneously in multiple regions. This ensures all of our customers across regions get the very latest Workato software updates.
Security is not negotiable
Protecting and securing our customers’ data is our #1 priority. At Workato, we take the security of your data very seriously. Security is top of mind when we design and implement our products, services, and everything we do at Workato. All Workato customers are always on the same version of our software. This gives us the freedom to innovate faster and the ability to protect our customers’ data reliably. We also operate on a unified security model. This includes user access, system integration, reporting, mobile devices, and IT access.
Workato platform supports key security and privacy concepts that promote a secure and safe environment for our customers.
- You own and control your data. You determine what data is accessed and processed by Workato. You have control over configuring how long Workato stores your data.
- Full data processing transparency. We provide you with visibility to our security and privacy controls through third-party audits (SOC-2 Type II), as well as our Customer Audit Program.
Enterprise-grade security is built-in
Workato provides a highly secure and reliable integration service using proven, tested, best-in-class technologies, practices, and procedures. Workato’s comprehensive approach to security covers application security, data protection, Workato infrastructure security, and more. The same enterprise-grade security is available across all the regions in which Workato has a data center.
Additionally, customers choosing to store data in any data center have access to all the standard security features:
Authentication. Workato uses industry-standard best practices for application security. Workato supports SAML 2.0 based authentication and Two-factor authentication.
Authorization. Workato supports flexible and fine-grained access control so the administrators can control access to Workato and what they can do within the shared Workato workspace.
Access. Workato services across all regions are accessible only over HTTPS. Unauthorized third parties cannot intercept traffic over these protocols due to encryption. Workato uses industry best practices for network security. Connections use TLS 1.2 (minimum) and only strong encryption algorithms with a key length of at least 128 bits.
Data encryption. Data “at rest” in the Workato database is encrypted using AES-256. Encryption adds an extra layer of protection against unauthorized access. Optionally, you can control your own encryption key, through integration with AWS KMS.
Data masking. Mask steps that may contain sensitive data like employee addresses or sales numbers. Data is not visible in the job details UI for the masked step. Masked data is not persisted in the job history database.
More to come
As a leading provider of enterprise automation cloud platforms, Workato uses cloud services to deliver a simple to use and powerful automation platform to forward-thinking companies. Our platform delivers industry-leading capability today and in the future. We are continually adding innovative updates to meet our customers’ needs and accommodating future changes to your businesses, security and compliance requirements.
For more information, check our documentation.